Connecting to the internet today is not just a matter of speed but also of trust. Networks handle more and more devices, sensitive data, and services that communicate almost constantly. This is why an approach called zero trust has emerged, where nothing is automatically considered safe. The article explains why this model was created and how it subtly influences everyday internet functioning.
The term zero trust may sound harsh, but it's really not about mistrusting everything. The basic idea is simple. Trust is not automatically assumed just because something is part of the network or system. Every access is treated as new and needs to be handled accordingly.
This perspective emerged when relying solely on connectivity or environment stopped making sense. The internet is no longer a single place nor a closed space. Access varies by device, service, and situation, and security had to adapt.
The zero trust model opposes automatic trust. It doesn't count on the network or connection itself creating a safe space. Trust is not a state that applies perpetually; instead, it's something that is continuously verified according to what's happening at the moment.
The term started being used in corporate environments where there was a need to better manage access to data and services. Over time, it became clear that this is not just a corporate issue but a general response to how the internet functions today. And that's why it's worth looking into why the original concept of trust in the network stopped being sufficient.
Why did the old trust model stop working?
For a long time, the internet operated on a relatively simple principle. There was the network and everything outside it. The network was considered a safe space, and the main control took place when someone was connecting. Once access was allowed, the system didn't check much what happened inside.
This approach made sense when working from a single location and limited number of devices. Most services were part of one network, and boundaries between the inside and outside world were relatively clear. If entry was monitored, the rest of the functioning wasn't as scrutinized.
But today's internet is not that clear cut. Data travels between various services, devices, and places. Access isn't tied to a single network or environment. Once someone gets 'inside', the system doesn't have many ways to know if they are behaving correctly. That's where the problem could really start.
The weakness of the old model lies not in the technology but in the assumption of trust. Once entire network trust becomes automatic, overlooking who actually accesses data and under which circumstances happens more often. And that's where it becomes clearer what zero trust means in practice. Trust is not lent to the space as a whole but rather to individual accesses.
How does zero trust function in practice?
In practice, this means access to services and data isn't given once and for all. Logging in from a known device usually happens without delay. The same account, but on a new device or from another place, may trigger further verification. This isn't an error but a reaction to a changed situation. This is commonly how zero trust functionality is expressed.
Similar principles apply to more sensitive operations. Reading content occurs without restrictions, but changing passwords or account settings requires extra confirmation. The system doesn't decide based on who's connected to the network but rather on what they're attempting to do at that moment.
Checks don't concern the entire network or all devices at once. They relate to specific access moments. If behavior follows a usual pattern, nothing changes. As soon as circumstances differ, access tightens.
Thanks to this, the zero trust model doesn't act as a constant limitation. It's mostly invisible, appearing only when something deviates from regular use.
Zero trust isn't just for companies; it concerns the regular internet too
The principles discussed here are no longer confined just to corporate systems. Regular users encounter them when using services they take for granted. Logging into the same account can vary every time, depending on where and how they access it.
From the user's perspective, this manifests subtly. Sometimes extra confirmation is required, whilst other times, a service reacts more cautiously to behavior changes. It's not by chance or system error but an effort not to make decisions based on a single signal. This is how zero trust principles gradually become part of regular internet usage.
Importantly, this approach is not applied universally. It doesn't concern the entire network or all devices at once. It always reacts to particular situations and specific actions. Thanks to this, the internet can remain usable while better reacting to things outside normal operations.

What does zero trust mean for households and smart devices?
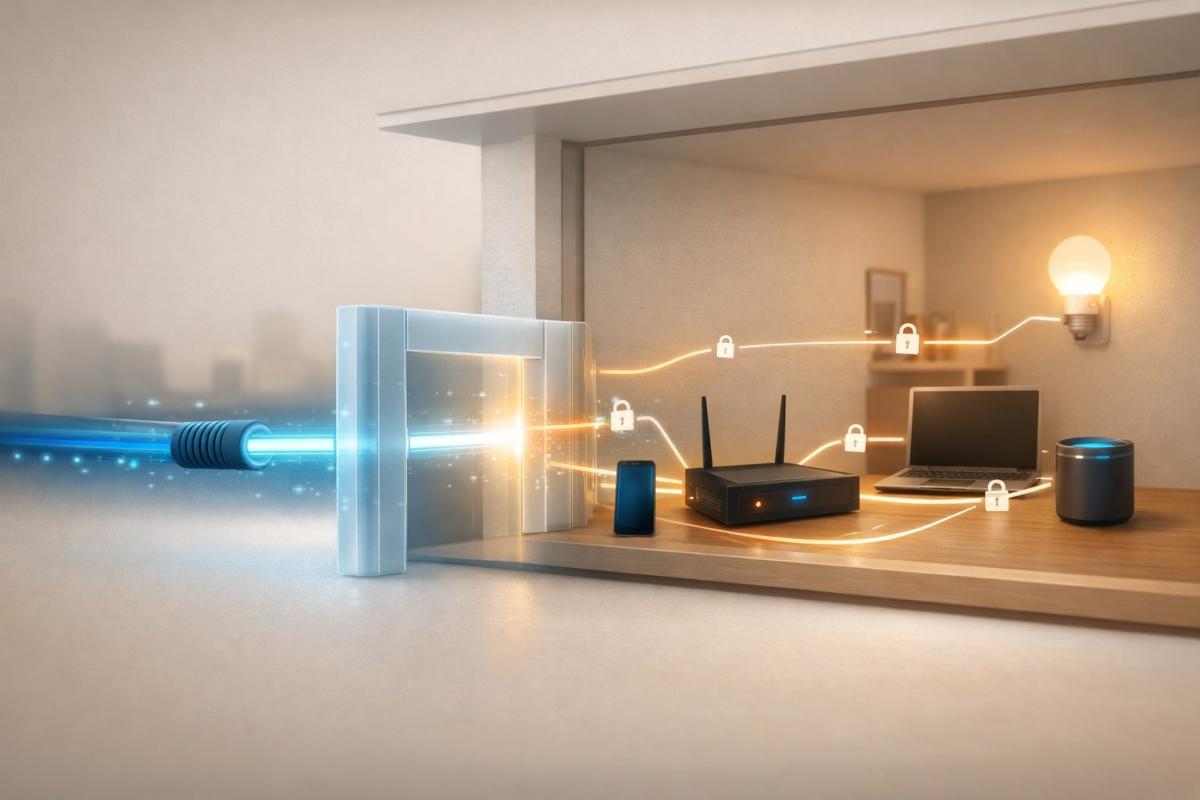
In households, the network functions more like a small ecosystem than a single connection. Besides computers and phones, TVs, speakers, cameras, vacuums, or thermostats are also connected. Each of these devices communicates differently, with different services and in different intervals.
Here, the difference in security approach becomes most apparent. Not all devices require the same permissions, and not all behave the same way. While a laptop or phone actively works with accounts and data, other devices merely send information at regular intervals or await commands. Judging them all the same would not make sense.
In practice, this means that individual roles of devices in a home network are increasingly addressed. What accesses externally, what only internally, what can change settings, and what should function more isolated. This approach reduces the risk of one device's problem affecting the rest of the household. This is how zero trust increasingly integrates into regular home environments.
From the user's point of view, it usually doesn't manifest in any dramatic way. More often, it changes how devices are isolated and how they communicate. The result isn't more complex handling but a network more resilient to errors and unexpected behavior of individual components.
Will zero trust bring more security or more inconvenience?
The issue of security and convenience is often pitted against each other in technology, as if one must necessarily detract from the other. However, this opposition is somewhat misleading with zero trust. It's not so much about tightening things up but rather about changing our expectations. We have accustomed to technologies being smooth, instantaneous, and ideally invisible. Whenever we are disturbed, we take it as a problem.
Yet, the comfort we've become used to originated when the internet was simpler and slower. Today, the digital environment is much closer to our privacy, decisions, and daily habits. The closer it is, the less sense it makes to rely on automatic. Zero trust brings a level of awareness into this. It reminds us that things have context, that circumstances matter, and that not everything has to pass without questioning just because it worked yesterday.
Inconvenience mainly appears when we expect the old world under new conditions. But if we accept that technologies are not neutral backdrops but active parts of our lives, this approach makes more sense. Not as a restriction but as a form of digital maturity. Just as we lock doors, even in peaceful neighborhoods, or look both ways even when the light is green.
Ultimately, zero trust doesn’t so much stand on the issue of security versus convenience but rather on how we want to continue living with the internet. Whether as an environment used as a matter of course or as a space where sometimes it’s worth slowing down and knowing who and what we’re giving access to.
What are AI agents and how can they help you today?

AI agents are no longer just an experiment of tech companies. They are increasingly appearing in tools we use every day and can independently plan, decide, and execute tasks. We explain what an AI agent is, how it differs from a regular chatbot, and where it can actually save you time and energy.
What is cache and how to clear it

The concept of cache appears in browsers, phone settings, and when troubleshooting websites, but few know what it exactly means. Cache aims to speed up data loading, but sometimes it can be rather a hindrance. Let's explain what cache memory is, how it works in practice, and when it's sensible to clear it.
digital carbon footprint: how the internet and online services burden the planet

Everyday online activities have a real energy footprint that quickly multiplies in total. In the article, we will look at what digital carbon footprint means, how much energy regular internet use costs, and which activities burden the environment the most. Areas where consumption is growing the fastest and impact is not immediately visible deserve special attention.
Is blue light really a problem? The answer isn't so simple

The topic of blue light has led to many simplifications and unnecessary fears. Blue light exposure before sleep is often discussed, but its impact is not limited to just sleep. Let's put things in context, separate facts from myths, and see when it makes sense to address its effects and when it is more about excessive concern.
Are you chatting with a human or a bot? How to identify AI in chat

Online chats are often handled by artificial intelligence today, and at first glance, the responses appear to be from a real person. This is especially true for customer support, where speed and fluency are key. We'll look at how to identify AI in chat, what signs you can use to distinguish it from a human, and where the line of recognition becomes very thin.
What is ransomware and why does it no longer threaten only large companies?

Ransomware attacks are among the most common cyber threats today and are no longer just a concern for large companies. Just one careless click can cost you access to your data. We'll explain what ransomware is, how it works, and why attackers are increasingly targeting average users and smaller businesses.